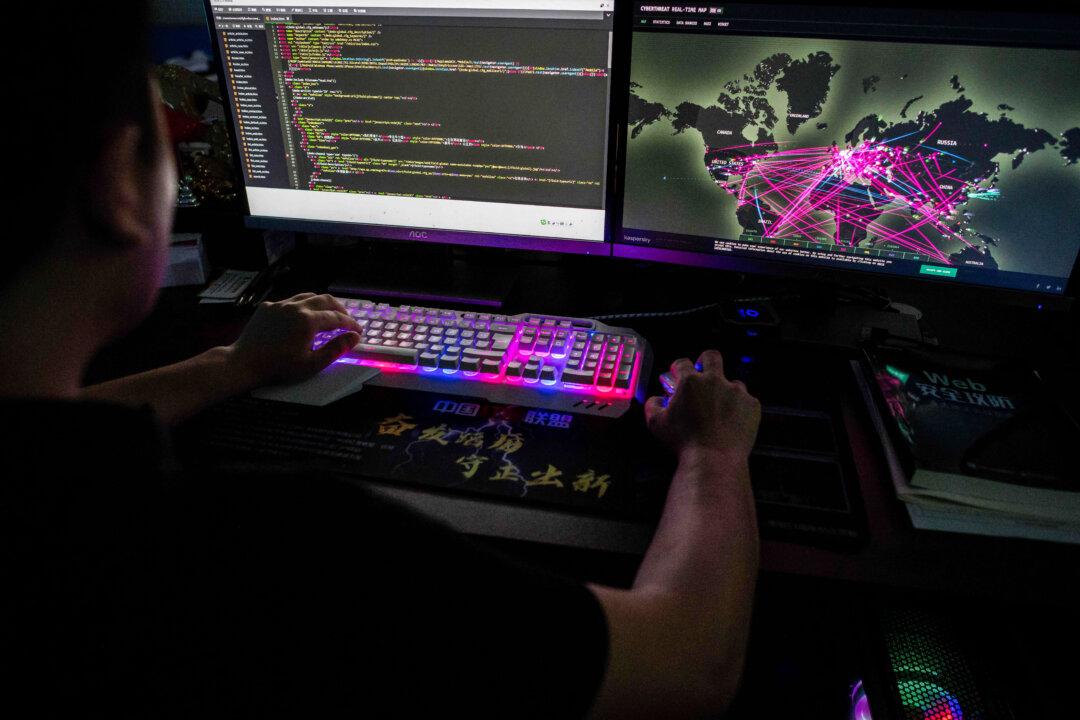
A ransomware group called “Ghost” is exploiting the network vulnerabilities of various organizations to gain access to their systems, according to a joint advisory issued by multiple U.S. federal agencies.
“Beginning early 2021, Ghost actors began attacking victims whose internet-facing services ran outdated versions of software and firmware,” the Cybersecurity and Infrastructure Security Agency (CISA) said in the Feb. 19 joint advisory. “Ghost actors, located in China, conduct these widespread attacks for financial gain.”